John Douglas's moving vocal performance on "Oranges & Apples" showcases an engaging mix of acoustic folk with a cinematic touch....
The 16 tracks on Nick Hudson's wide and ambitious album "Kanda Teenage Honey" show his skill as an avant-pop musician....
Invited guests mingled enthusiastically with cast and crew of the Australian-produced, New Zealand-helmed movie Anno 2020 at its world premiere...
The instrumental song "I Remember" by Ohnarp Janson is a lovely trip through the world of gentle jazz, complete with...
The intriguing combination of electronica, soft rock, and futuristic synthwave on Eric Lanz's "Acteurs du Monde" takes listeners to a...
The latest song from SkyCall, "Wendy," features a promising sound revealed by Fabrice Duval, the neuropsychiatrist turned "rockstar" from Colmar,...
With a genuine rock feel influenced by bands like Oasis and Girls Against Boys, Quiz Show's "China Glaze" is a...
"Nightmare" by Deadly Shadows is a compelling classic metal track that pays homage to the genre's roots, drawing inspiration from...
The interesting "Gephard" EP by Bahnhof Motte explores a wide range of musical influences. It skillfully integrates elements of progressive...
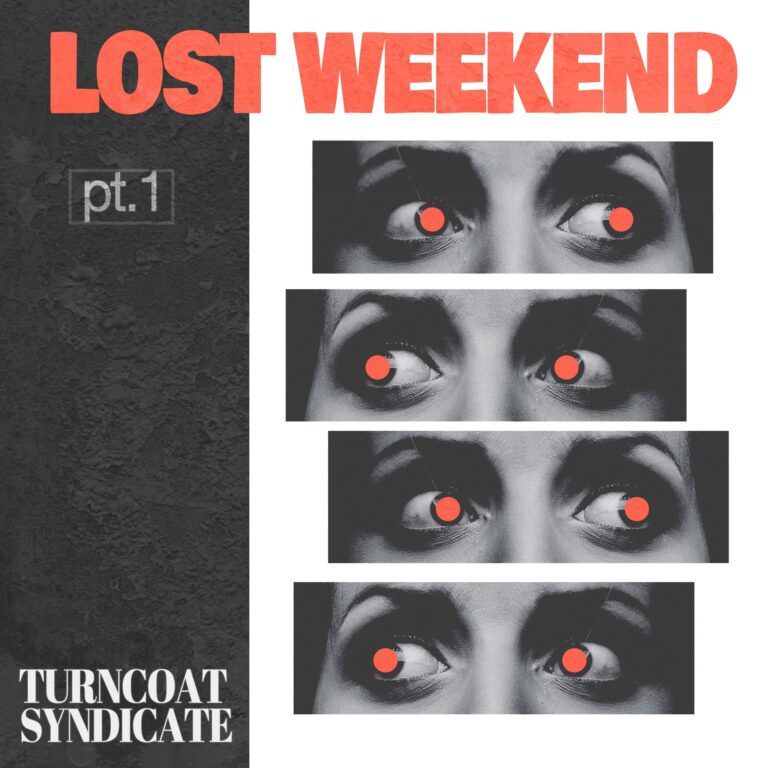
Turncoat Syndicate's "Past Mistakes" is a catchy indie rock song that explores reflective thinking and offers a balanced combination of...