"Rockin' Bach" by Glass Jones Piano is a masterful instrumental piano track that pushes the boundaries of classical piano into...
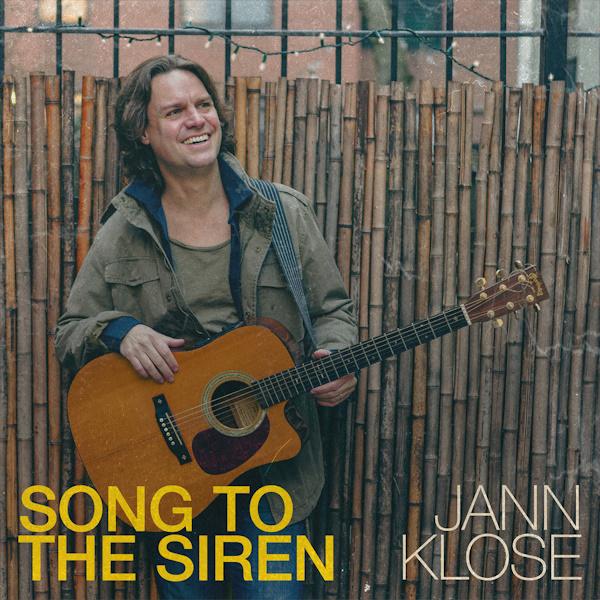
Award winning singer, songwriter and podcaster Jann Klose is releasing new music this season. His cover of Tim Buckley’s legendary...
Located in Stockholm, Then Comes Silence is a post-punk band with a strong gothic influence that keeps making waves in...
The Shadow Majlis' "Deer In The Headlights" is an engaging combination of experimental rock and world music elements, with creative...
John Douglas's moving vocal performance on "Oranges & Apples" showcases an engaging mix of acoustic folk with a cinematic touch....
The 16 tracks on Nick Hudson's wide and ambitious album "Kanda Teenage Honey" show his skill as an avant-pop musician....
Invited guests mingled enthusiastically with cast and crew of the Australian-produced, New Zealand-helmed movie Anno 2020 at its world premiere...
The instrumental song "I Remember" by Ohnarp Janson is a lovely trip through the world of gentle jazz, complete with...
The intriguing combination of electronica, soft rock, and futuristic synthwave on Eric Lanz's "Acteurs du Monde" takes listeners to a...
The latest song from SkyCall, "Wendy," features a promising sound revealed by Fabrice Duval, the neuropsychiatrist turned "rockstar" from Colmar,...